Secure Flash Programming is an optional feature that reduces the risk of intellectual property being pirated during the production process. Using breakthrough, proprietary technology, Softlog System’s Secure Flash Programming protects against piracy at the manufacturing plant.
Available with every programmer that we sell, Secure Flash Programming introduces several layers of protection for your business-critical intellectual property.
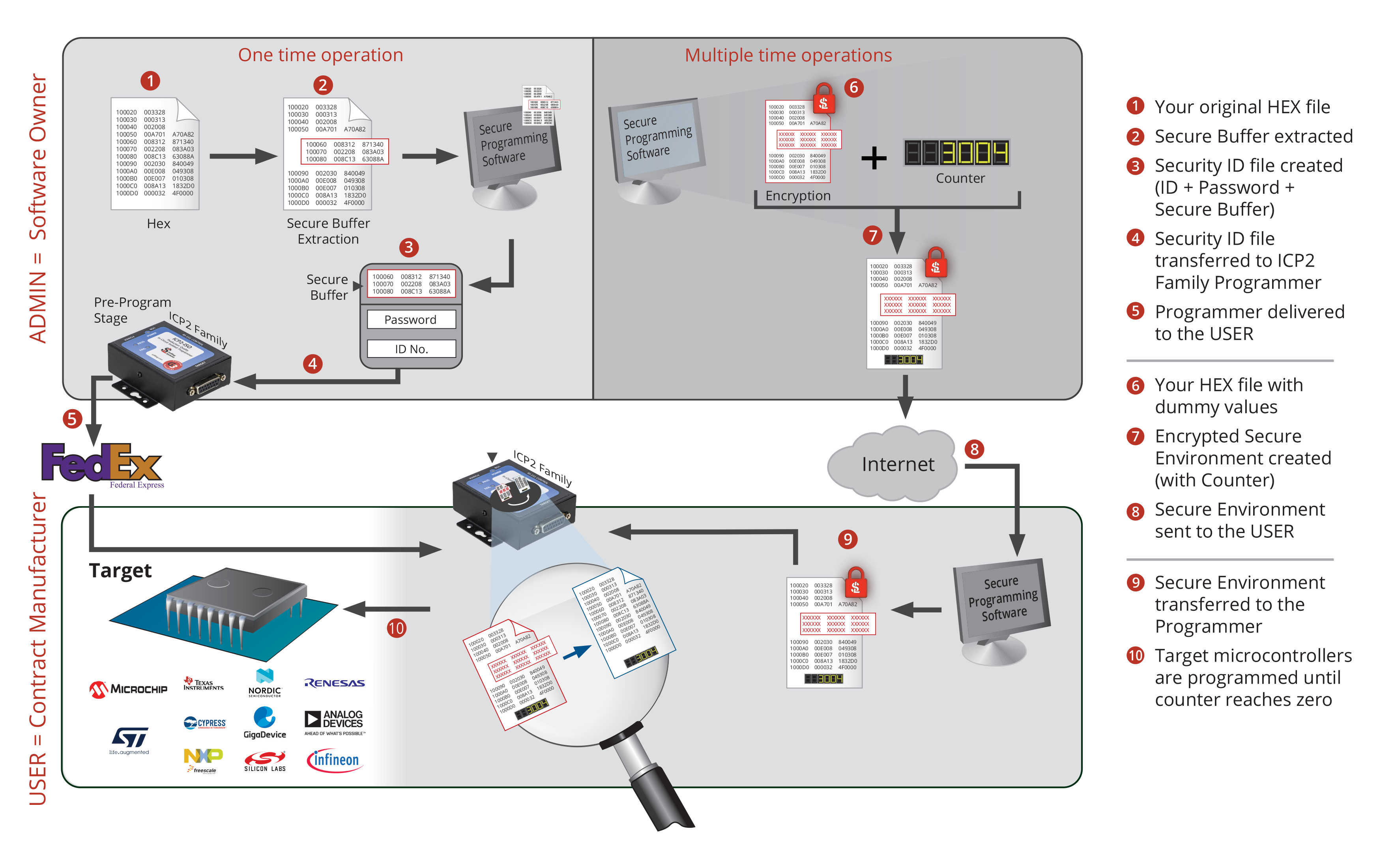
Softlog Systems starts protecting your Hex file before it ever reaches the manufacturer. We help you extract a security buffer from the hex file, and using our software GUI, upload the password-protected firmware to the Softlog programmer. The programmer can then be safely sent to the production facility.
Next, you’ll create an environment file that contains the hex file with dummy values and configuration information. Secure Programming software encrypts the environment file using an encryption algorithm and adds an optional counter to limit the amount of successfully programmed devices. This creates an encrypted secure environment that can only be accepted by the password-protected programmer unit. The encrypted secure environment file can be sent electronically to the production facility.
At the production facility, the encrypted secure environment file is uploaded into the programmer. The programmer validates the file and replaces dummy values with real values from the security buffer. This creates a production file image that is only available for the specific programmer unit and, if activated, has a predefined counter to prevent spillage. The programmer programs devices until the counter reaches zero.
Secure Programming operates on two levels. The “Admin” level corresponds to the developer or owner of the software, while the “User” level corresponds to a contract manufacturer (CM) or other personnel authorized to program devices. Security-sensitive tasks are only performed at the Admin level. Using the Softlog GUI, the software owner initializes the programmer with a unique password, ID number and secure buffer prior to shipping it to the CM. The owner can update the programmer remotely by sending encrypted files to the CM.
At the outset of a programming run, the owner creates an environment file that includes hex data, configuration information, and an optional counter that limits the number of successfully programmed devices. Secure Programming encrypts the environment file using strong encryption algorithms. This file can only be decoded by a programmer that has been initialized with the correct password and ID number.
An optional counter, stored in non-volatile memory of the programmer, ensures that the number of programmed devices does not exceed a pre-defined value. This limits the number of devices that can be programmed from a particular environment file, thus preventing gray/black marketing of “spoofed” products.
Join our newsletter and get exclusive industry insights, product updates, and expert tips on in-circuit programming and secure MCU solutions.
🔹 Be the first to know about new supported devices
🔹 Get expert advice on optimizing your programming workflow
🔹 Access exclusive offers and technical resources
👉 Sign up now and stay ahead in microcontroller programming!